With Metric Insights Trusted Server Authentication, it is possible to allow users of an internal web application to login to Metric Insights automatically through a proxy url. The primary purpose of this facility is to to integrate Metric Insights with an existing web application.
EXAMPLE
A common use case for this capability is if you have already developed an internal web portal for customers or employees. These customers and employees have already logged into your web portal, and you want those logged in users to automatically have access to Metric Insights as well.
NOTE: The format of the External Application Editor is slightly different in Version 3.
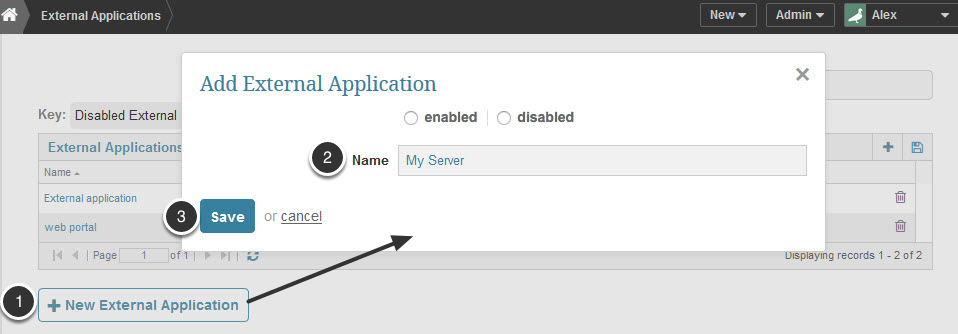
1. Access list of existing 'External Applications' from Admin > Credentials > External Applications
- Click [+ New External Application] to access a pop-up
- Enter an application Name (for example, 'My Server')
- Save your entry.
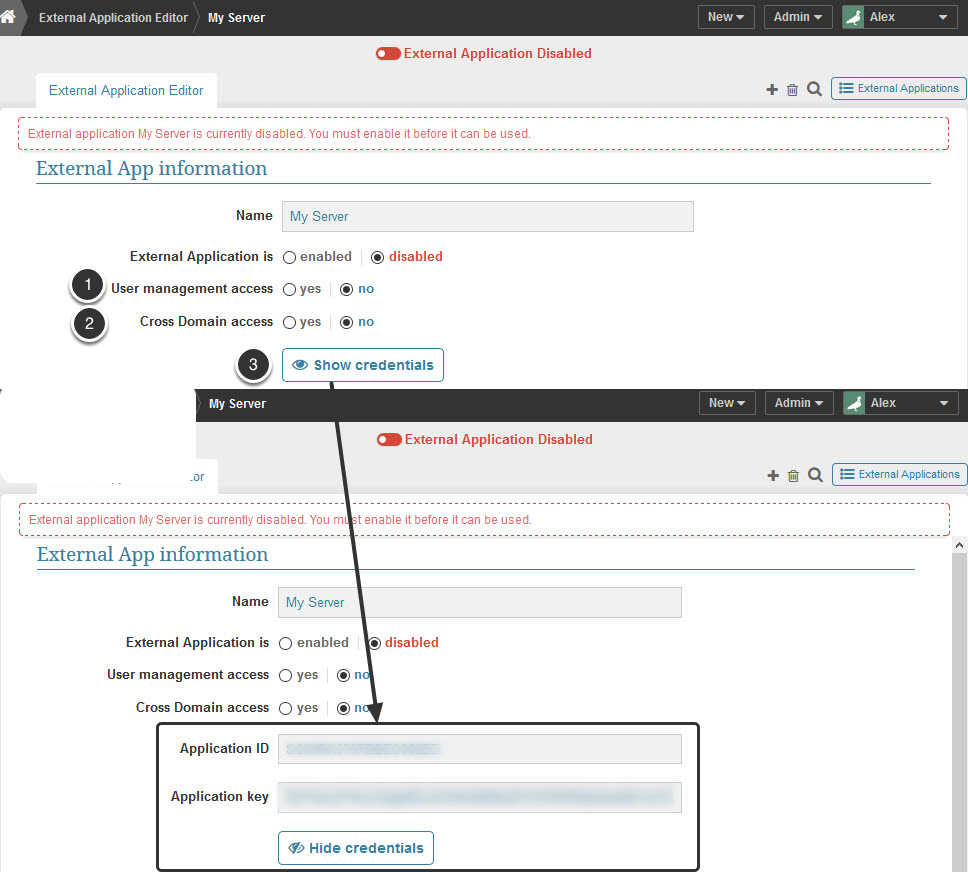
The External Application Editor opens.
2. Complete Definition of the External Application
- User Management Access: Set to 'yes' to integrate MI with LDAP to allow your application to add/modify MI users via API calls; retain the default 'no' value if you do not plan on writing code to sync MI users with your portal
- Cross Domain Access: Set to 'no' unless you know you are going to be using the Metric Insights JavaScript API for low level access to charts and chart data
- Click Show Credentials to request MI to generate the Application Id and an Application key. Both values are needed when developing your portal
3. Log in by proxy
Your web application will login to Metric Insights with the following steps:
- Using the MI username, and the application id and application key obtained above, request an authentication token with an HTTPS POST to https://company.metricinsights.com/api/get_ticket. The required POST variables are 'user', 'application_id', and 'application_key'.
- Parse the returned json object: {'ticket':'<ticketValue>'}
- Redirect the user to https://company.metricinsights.com/ticket/<ticketValue>/<RELATIVE_MI_URL> where RELATIVE_MI_URL is blank for the MI dashboard, or pointing to a specific MI element.
See the 'Example proxy endpoint in PHP' section below for more information
3.1. Example proxy endpoint in PHP
For example, this proxy script could live under https://yourportal.com/mi.php and whenever you wanted to link to https://company.metricinsights.com/<RELATIVE_MI_URL>, you would instead send your users to https://yourportal.com/mi.php?url=RELATIVE_MI_URL. The sections in bold would need to be edited for your organization.
<?php
define('BASE_URL','https://company.metricinsights.com');
define('APPLICATION_ID','<external application id>');
define('APPLICATION_KEY','<external application key>');
$ch = curl_init(BASE_URL.'api/get_ticket/');
curl_setopt($ch, CURLOPT_POSTFIELDS, array('application_id'=>APPLICATION_ID,
'application_key'=>APPLICATION_KEY,
'user'=>'<the logged in user's MI username>'));
curl_setopt($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_HTTPHEADER, array('Accept: application/json'));
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$response = curl_exec($ch);
$tmp = json_decode($response, true);
$ticket = $tmp['ticket'];
header('Location: '.BASE_URL.'ticket/'.$ticket.'/'.(isset($_GET['url'])?$_GET['url']:''),true,302);
exit;